-
Resurrection of the weblog
After getting a new version of Jekyll installed, pulling some archives from Github, and some from the Internet Wayback Machine, I think I have most of my posts back. I need to do some adjustments to a few of the templates, but I think we’re back and running well enough. There may be some older posts that I’m missing, but I think they’re fine being lost to the ether.
-
When you have fun learning

-
From one challenge and into another
-
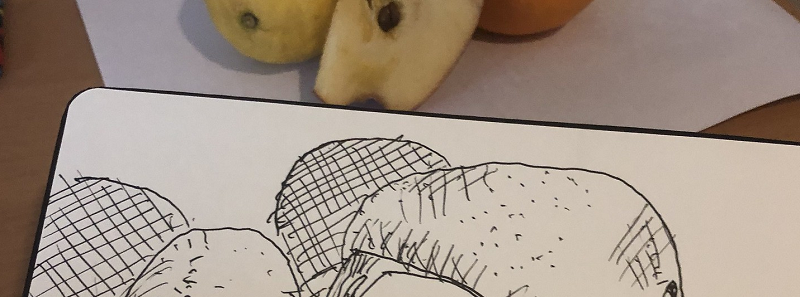
Giving the Every Day in May challenge another try
-
Using the Flask-RESTful library
In my last post, I wired up a very simple API server in Python with Flask. This time, I’ll add in a library meant to make building APIs a bit easier: Flask-RESTful.